-
 +32 +2
+32 +2The solution to the Voynich manuscript | Nicholas Gibbs
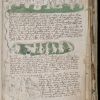
For medievalists or anyone with more than a passing interest, the most unusual element of the Voynich manuscript is its handwritten text.
-
 +17 +1
+17 +1Five Eyes Unlimited
What A Global Anti-Encryption Regime Could Look Like. By Danny O’Brien, EFF.
-
 +15 +1
+15 +1Big scientific breakthrough at sub-atomic level holds promise for secure comms
Chinese scientists have pulled off a major feat with one of the sub-atomic world's weirdest phenomena: photons that behave like twins and experience the same things simultaneously, even over great distances.
-
 +12 +1
+12 +1In Trump’s America, Black Lives Matter activists grow wary of their smartphones
A movement born on social media begins to fear that technology is making it vulnerable. By Craig Timberg.
-
 +25 +1
+25 +1Wikipedia’s Switch to HTTPS Has Successfully Fought Government Censorship
Harvard researchers found fewer instances of Wikipedia censorship after the site started encrypting all of its traffic. By Daniel Oberhaus.
-
 +16 +1
+16 +1The world’s most mysterious book - Stephen Bax
-
 +17 +1
+17 +1I Am A Number. Am I Prime?
On the search for an efficient algorithm to tell if a number is prime. By Kaneenika Sinha.
-
 +9 +1
+9 +1Quantum counterfeiters might succeed
Physicists demonstrate security issue with quantum cash. By Emily Conover.
-
 +21 +1
+21 +1Phone-Cracking Cellebrite Software Used to Prosecute Tortured Dissident
Like any good, vaguely sinister spy outfitter, Cellebrite deflects questions about whether it would sell its phone-breaching tools to a repressive regime. By Sam Biddle, Fahad Desmukh.
-
 +39 +1
+39 +1Future of Privacy, The
The world’s best-kept secrets — those of private citizens and state institutions — will one day sit in plain sight. By William Gibson.
-
 +35 +1
+35 +1The Unsolvable Mysteries of the Voynich Manuscript
Some of the greatest code breakers in history have tried to unlock the mysteries of the Voynich Manuscript. No one has succeeded. The word “ink” is a child of the Latin incaustum, which means “having been burned.” In the Middle Ages, people thought that ink burned its way into parchment, because iron-gall inks go onto the page pale, then darken. This is not what’s happening, physically, but it makes sense as a metaphor: a medieval manuscript, because it was made by hand...
-
 +13 +1
+13 +1Trump’s CIA Director Pick Thinks Using Encryption ‘May Itself Be A Red Flag’
He also has almost no experience in the world of intelligence. By Lorenzo Franceschi-Bicchierai.
-
 +43 +1
+43 +1If The FBI Can’t Stop All These Leaks About An Investigation, Why Would it Be Able To Keep Encryption Backdoor Secret?
Basically, the FBI (and the DOJ) were leaking information like it was the last chance they’d ever have to leak information and their lives depended on who could leak the most. And, remember, this is the same damn agency that is so insistent on forcing tech companies to put backdoors into any encryption to make sure the FBI can get into anything it wants… By Mike Masnick.
-
 +4 +1
+4 +1DKIM Verification Announcement on Wikileaks
Domain Keys Identified Mail, or DKIM, is a highly regarded email security system that can be used to independently authenticate the contents and sender of an email that uses it. DKIM was developed and is widely deployed as an email server anti-spam mechanism, including on Gmail.com and HillaryClinton.com. DKIM-enabled mail servers cryptographically sign the emails they relay so that the recipients’ mail servers can authenticate them. DKIM has the beneficial side-effect of causing messages to become "cryptographically non-repudiable"; that is, after the email has been sent, the sender cannot credibly repudiate the message ...
-
 +8 +1
+8 +1John Podesta Was Warned in 2008 to Start Encrypting Sensitive Emails
Denis McDonough, now White House chief of staff, wrote in 2008 that he was surprised to see "a sensitive doc bumping around on public email addresses." By Dan Froomkin.
-
 +13 +1
+13 +1German magazine “konkret” interviews Yasha Levine about Tor, spies and the cult of crypto
German leftwing magazine konkret published an interview with me on the the dark origins of the Tor Project, Jacob Applebaum and the normalization of sexual abuse inside the privacy community, the rightwing origins of the cult of crypto, the corruption of Internet activism, and lots of other topics.
-
 +28 +1
+28 +1China’s quantum satellite could make data breaches a thing of the past
The Micius satellite will encrypt data using fundamental laws of physics rather than crackable codes. By Robert Young.
-
 +13 +1
+13 +1NSA could put undetectable “trapdoors” in millions of crypto keys
Technique allows attackers to passively decrypt Diffie-Hellman protected data. By Dan Goodin.
-
 +7 +1
+7 +1Jane Fawcett, British code-breaker during World War II, dies at 95
She deciphered a German message that led to one of Britain’s greatest naval victories, the sinking of the battleship Bismarck. By Matt Schudel.
-
 +14 +1
+14 +1Senator: let’s fix “third-party doctrine” that enabled NSA mass snooping
Q&A: Ars sits down with Oregon’s outspoken advocate of strong crypto, Sen. Ron Wyden. (Apr. 3)
Submit a link
Start a discussion